1) I Hate March Madness...
...but this is fun.
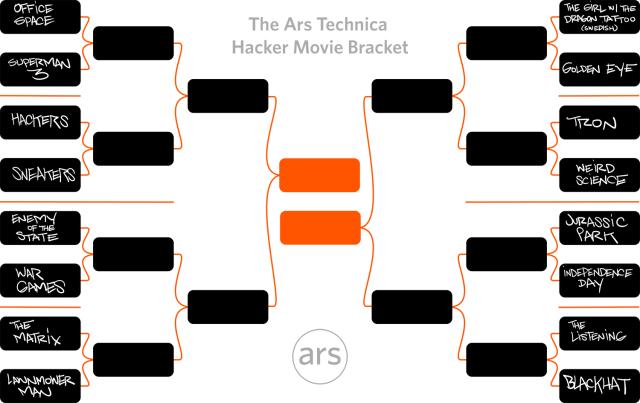
Ars Technica is doing college basketball style brackets for Hacker Movies.
Perhaps unsurprisingly, I am rooting for Sneakers to go all the way.
A common topic of discussion in our house, now that my wife works for UpWorthy is the idea that hate makes just as much money for content creators on the internet as "likes". Any time you share something to say to your friends "hey look how dumb this is" you are generating clicks and upranking links for the person you are disliking. Any time you link to a page, share it, like, or otherwise draw attention to it, you are just driving more traffic to that site and therefore more money into the pockets of the creator of the content you purport to dislike.
That's right: Trolling just makes the people you oppose have more visibility and more money!
Of course, there are a few ways around that. One simple way is to just not share your hate, keep it to yourself. Another is to do a screen-cap of the content you so dislike and share it that way (just remind your fellow haters not to go post comments on the original blog entry, forum, or facebook post, since that's just driving traffic and giving them more money).
Another trick is to use services like doNOTlink. This site is a URL shortener (similar to bit.ly and many other), but it adds a nofollow attribute to the link, and also blocks search engine robots from crawling the link. Short version, it lets you share things without increasing their search ranking.
You could also add the nofollow attribute to your embedded links manually. If you are on WordPress (I very strongly recommend against using WordPress for anything), there is also nofollow a plugin to simplify doing this.
3) Samba Dropped the Beat...
If you've ever tried to make a Linux system talk to a Windows one, then you are probably familiar with Samba. If you haven't had to attempt this, then good for you. For those of you not so blessed, be warned that a serious vulnerability has been found in the Samba daemon (smbd) that can be exploited for arbitrary code execution. For once no blame can be placed on Microsoft, this is strictly a Samba problem.
A malicious Samba client can exploit the security hole by sending specially crafted packets to a vulnerable Samba server. This allows an unauthenticated attacker to execute arbitrary code with root privileges.
The vulnerability has been addressed with the Samba 4.2.0rc5, 4.1.17, 4.0.25 and 3.6.25 security releases. Patches for older versions of the software have also been made available by Samba. Security updates have been released for Red Hat, Fedora, Ubuntu, Debian, and SUSE.
If you want to know more, Red Hat's security team did a detailed analysis.
4) Why you should not piss off the internet...
Last time I mentioned the kerfuffle involving Lenovo pre-packaging an HTTPS bypassing adware on their laptops. Well, Lenovo has been subject to the standard recompense for being jerks to users in the internet age: their website was hacked.
The attack was carried out by the now infamous Lizard Squad, who are often not really on the side of the average consumer, but I have to give them props for this one. The attackers modified DNS records in Lenovo domain registrar accounts in an effort to redirect users to defacement pages. The hackers replaced the regular nameservers with CloudFlare IP addresses. Experts believe this was done in order to obfuscate the IP address of the destination server and to balance the traffic load to the website. CloudFlare acted quickly to restore services.
The attackers also changed mail server records allowing them to intercept messages sent to Lenovo email addresses. Lizard Squad has published screenshots of two intercepted emails on Twitter. The hackers said they might publish other “interesting” emails later.
The attack targeted at Lenovo shows that malicious actors don’t necessarily need to gain access to an organization’s corporate servers to cause damage. OpenDNS advises website owners to change their passwords frequently and, when possible, enable domain locking to avoid such redirections.
No comments:
Post a Comment